Last month a vulnerability was discovered in the Fancybox for WordPress plugin, making it possible for a hacker to inject an iframe into the website without needing administrator access. Although the issue was promptly patched, a string of seemingly random WordPress websites were recently compromised using this vulnerability.
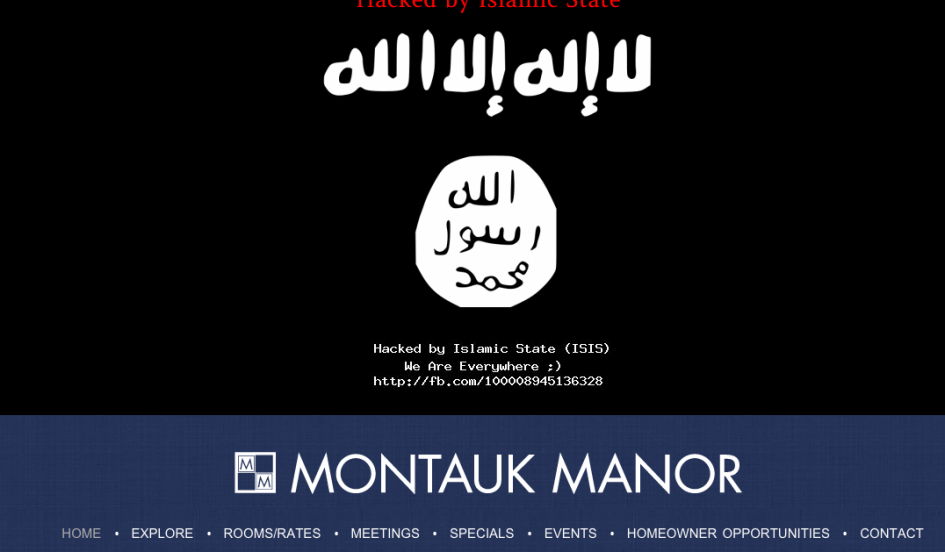
Hackers claiming to be acting on behalf of ISIS exploited Fancybox to deface the websites with propaganda for the terrorist group. Credit Union Journal reports that a Montana credit union website was attacked using the Fancybox plugin as the entry point.
Area43.net examined the cached Google source code for several other hacked sites and reported that both Eldoraspeedway.com and Montgomeryinn.com have since removed the Fancybox for WordPress plugin.
In order to deface the websites, the suspected ISIS hackers likely scanned for sites that have not updated the Fancybox for WordPress plugin, as the sites bear no other commonalities apart from using WordPress. Many major news outlets with no understanding of WordPress’ plugin system have wrongly attributed the security flaw to WordPress itself.
Fancybox for WordPress is currently active on more than 100,000 sites, but stats on WordPress.org do not break down how many of those are using a version older than the patched update issued in February. WordPress.org did not push out a forced update for the Fancybox plugin vulnerability. Any website owner running this plugin who has not checked for updates within the past month, is probably still using a vulnerable version of Fancybox for WordPress.
What is it going to take for WordPress site administrators to keep their plugins updated? If you’re not comfortable updating WordPress plugins yourself, then you need to be on a maintenance plan with a development company to keep your software updated and secure.
While many developers are not too keen on the possibility of WordPress someday adopting automatic updates for core, plugins, and themes by default, your average website owner would probably probably prefer it over would-be ISIS hackers exploiting the simplest of vulnerabilities to deface their websites.
Source: WP Tavern